28 December 2023 • Cyber security

Phishing simulations are a standard practice for many organizations. And rightfully so.
The number of phishing attacks has increased by over 150% every year since 2019. In 2022, APWG logged over 4.7 million phishing attacks. According to research by the FBI, phishing scams account for almost 22 percent of all data breaches that happen.
To combat this, many organizations opt for phishing simulations to test the susceptibility of their employees.
However, we believe (and research now shows), that most organizations are not helping their employees with their phishing simulations. In fact, they’re even making them more vulnerable to phishing.
In this article, we’ll explain our vision of why most phishing simulations are doing more harm than good and how you can prevent that from happening.
Issue #1: templated emails don’t prepare employees for spear phishing
Many security officers opt for a phishing simulation strategy based on regularity and efficiency. This means they want their employees to be put to the test often, but don’t want to spend a lot of time putting the simulations together. The goal is to automate the process as much as possible.
If you look for phishing simulation providers across the internet, you’ll see that a lot of them play into this sentiment. They offer templates, AI-generated phishing emails, and automatically sent emails. This helps security officers check off ‘phishing tests’ from their to-do lists without breaking a sweat. Mission accomplished.
However, these templates are not preparing employees for the dangers of spear phishing.
Spear phishing is a phishing method where phishers research their target carefully. The attack therefore seems to come from a trusted source in the target’s life. They use the information they have gathered and social engineering techniques to then get the target to click on a malicious link.
Imagine a cyber criminal hacks the email address of one of your suppliers. In one of the emails, they find exactly which products they are expected to deliver and what the invoice looks like. All they now have to do is copy the invoice, change the bank account details, and send it over to your finance department from an email address that your finance department trusts. This is much harder for your employees to recognize as phishing than a standard template.
Spear phishing emails are much more difficult to spot for targets. And since templated phishing simulations don’t use these techniques, they’re simply not preparing your employees for the real cyber risks that they face. At best, they give both the security officer and the employees a false sense of security. The devil is in the details when it comes to phishing, and you can’t automate that sort of attention to detail.
Issue #2: phishing simulations combined with voluntary training are ineffective
Recent research shows that the combination of a phishing simulation with voluntary training doesn’t make employees resilient against phishing, but more often makes them more susceptible to clicking phishing links. This contradicts all prior research and a common industry practice.
So what does that common practice look like?
First, all employees are sent a phishing email. When somebody clicks a link, they are forwarded to a training page. Here they get voluntary training (meaning, they can simply choose not to do it) about what just happened and how they can spot phishing in the future. The idea is that when somebody has just been phished, they will be more open to training, and knowledge retention will be at its peak.
However, research now suggests that phishing simulations combined with voluntary training are ineffective. There are a few possible reasons for this:
- Employees feel like they have ‘learned their lesson’ after a phishing simulation, but don’t partake in voluntary training
- Employees who don’t click a link during a phishing simulation don’t get any form of security training whatsoever
- People may not retain training information well right after they feel ‘caught’ during a phishing simulation
- Employees require regular training to become truly aware and knowledgeable about cyber risks such as phishing
How to do phishing simulations the right way
We’ve now established that there are two major issues with how phishing simulations are often done today:
- Templated emails are not preparing employees for spear phishing
- Phishing simulations combined with voluntary training are ineffective
For the past year, we’ve been working with business owners, security officers, and other people responsible for security within organizations to solve this.
We are now offering spear phishing simulations. During this simulation, we will work with an organization to develop phishing emails that will seem authentic and trustworthy to all targeted employees. This could be by emulating an email from an HR software tool that the organization uses.
This is a more time-consuming effort than working with templates. But we believe in a quality over quantity approach. If a cyber criminal is going to invest time in hacking you, you should take the time to train your employees. You can’t automate everything. Because of this, we advise only doing a spear phishing simulation once or twice a year.
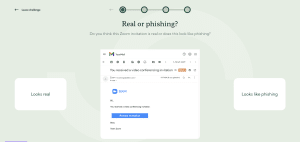
Aside from that, we offer a security awareness game that teaches employees how to recognize and act in the face of cyber threats, including phishing. Every week, employees get to take on a cyber security challenge that takes up to three minutes to complete. This helps them to build up knowledge and stay aware of cyber threats each day of the week.
In the game, each user starts a fictional organization. By doing challenges, they can make money for their business and improve its reputation. But if they get questions wrong, they lose money, and their reputation tanks. In the leaderboard, they can see which colleagues are scoring the most points. This creates a fun competitive element and boosts participation.
The security awareness game trains your team’s knowledge and the spear phishing simulation tests their susceptibility over time.
📚 Learn how Roosevelt Kliniek trains phishing awareness with Guardey
Protect your organization from phishing with Guardey
We firmly believe that you can’t automate phishing prevention. It takes regular training and targeted spear phishing simulations to truly make your employees resilient.
If you’re interested in trying our solution, feel free to schedule a demo.